Oh no! It's spam once again.
We've all discovered it-- whether it's a remark, through email, or the web browser; numerous sorts of spam require to be quit.
In this post, by specialists at leadingdigital marketing companyyou will know the 6 sorts of spam that need to be stopped quickly.
Allow's get begun.
Just how does spam impact our electronic life?
Everybody despises spam, right? It is frustrating to obtain on a personal degree, yet it's additionally rather negative for organization. From an advertising and marketing viewpoint, spam is troublesome because it interrupts productive relationships in between customers and the organizations in which they reveal legitimate interest.
Inboxes are usually obstructed with junk as well as advertising and marketing messages when it pertains to email, which makes it difficult for customers to receive the newsletters and various other interactions they request.
In general as digital marketing companysays that on the net, people have ended up being so inundated with marketing material-- specifically on social media sites sites-- that individuals are sidetracked from material that might offer them with genuine value.
It can be bothersome as well as hazardous to click on links in spam emails or posts, as they might take you to viruses as well as other hazards.
As long as we would certainly like it to, spam doesn't need to be a part of our digital lives. When we recognize the circumstances in which it can recognize and also show up spam when we see it, we can take targeted actions to eliminate it without harming our chances of obtaining beneficial emails from people we wish to speak with.
We've highlighted a few of the most common kinds of spam below.
Email spam
Email spam has actually constantly been an issue for organizations looking for to advertise their service or products. In the past, many organizations made use of an easy email address for their marketing campaigns.
As specialists at leadingdigital marketing companywill certainly inform you that it was a smart idea considering the majority of people do not wish to provide their e-mail addresses. It also led to even more spam e-mails due to the fact that spammers knew that the email address was openly offered.
This is why you should never ever pick an e-mail such as info@yoursite.com or help@yoursite.com, as these are conveniently validated by spammers and can cause spam issues.
Spam is an umbrella term for many kinds of unwanted email messages, consisting of:
Phishing: Messages that fool you into quiting personal details, such as passwords as well as usernames or charge card numbers.
Malware or infections: Messages containing software that can damage your computer or take control of it without consent.
Unrequested industrial e-mail (UCE): Also known as bulk e-mail, these are messages sent wholesale by a specific or business without approval and also often include deals for products or services that may be prohibited, fraudulent or deceitful.
Email harassment: These are generally obscene, threatening or offensive messages sent repetitively to an individual with whom the sender has no partnership. This additionally consists of sending bugging messages utilizing somebody else's name without permission (e.g., "spoofing").
Popular email spam subjects
Pharmaceuticals
The pharmaceutical sector is among the most preferred spam topics. Drug spam frequently includes fake Viagra, Cialis as well as various other drugs.
Drug spam may include fraudulent deals to offer prescription medications or counterfeit medications or distribute totally free prescription medication samples. These emails may additionally contain web links to web sites designed to look like legit on the internet pharmacies yet are infected with malware that can take personal information from the visitor's computer system.
Fraudsters also target pharmaceutical firms since they're usually happy to pay huge bucks for leads on new customers who experience various illnesses and problems that need normal treatment with their items. The more leads you can supply them, the far better your chances of making some money from them.
Drug spam is commonly sent out by spammers in Asia, who use cost-free webmail solutions like Yahoo! Mail to send out e-mails through multiple accounts.
A pharmaceutical spam project can be really successful for cyberpunks who have already acquired valid email addresses as well as recognize exactly how to spoof their IP addresses.
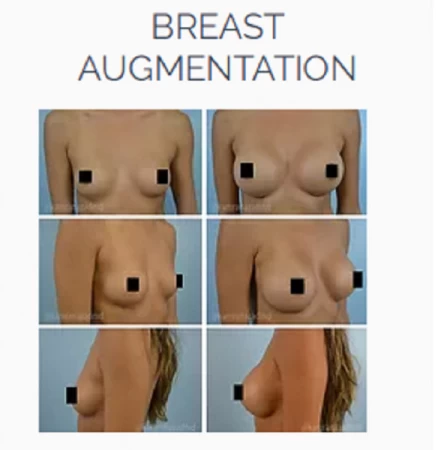
Adult content
A lot of people obtain emails from adult websites or grown-up dating services These emails usually include images of scantily dressed ladies and promises of open door to explicit web content if you sign up for an account.
Do not succumb to them-- these e-mails aren't from reputable firms, and they're just attempting to obtain your individual details so they can sell it to 3rd parties for marketing purposes.
Financial solutions.
These e-mails inform you how to generate income swiftly. They may ask you to send cash to obtain even more money or a big quantity of money. They may likewise ask for individual info, like your checking account number or social security number.
The subject lines for these emails frequently include words like:
" How to earn $1,000 monthly easily."
" Make $3,000 each week legitimately."
" How I made $10,000 in just 15 days."
This e-mail will have a web link that reroutes you to a site that can infect your computer system with malware or swipe your individual details.
You won't have the ability to earn money by adhering to the instructions in this e-mail, however you can lose money if you fall for it!
work-from-home jobs
You've possibly been targeted by a work-from-home rip-off if you've ever gotten an e-mail that assures you can make money from house.
A work-from-home work has actually been among the top frauds since covid time. It's so preferred since it appeals to the largest possible audience-- any person who intends to make money without leaving your house can succumb to this rip-off.
The fraud works by sending hundreds of e-mails motivating people to make an application for a work at their business. The e-mail guarantees a high wage and also simple work, without experience necessary. You need to complete an application and send it back with your checking account information as well as various other information.
The reality is that there are no work readily available with these firms-- they merely desire your details so they can swipe your cash or commit identification theft.
Exactly how do I know that the e-mail I obtained is spam?
If you're getting an email from a person you don't know, or if you really did not ask to receive it, after that maybe spam.
Check the sender's email address against any personal digital assistant you may have. It might be spam if the sender is not discovered in your address publication.
The subject line is deceptive or vague. Spam is designed to get your attention, so inspect the subject line of any type of email you obtain very carefully prior to opening it. Do not open it-- just delete it if it doesn't make feeling to you or appears questionable! As an example, "Re: your account balance", "You have actually won! or "You have actually won a lotto game"
Check out how long ago the message was sent. It could be spam if it were sent out greater than 2 weeks ago.
If you get an e-mail that looks like spam yet isn't originating from an obvious resource like Hotmail or Gmail, checks whether what's inside really associates with what's written in the subject line.
The sender asks for individual info like passwords or charge card numbers. , if a person asks for this kind of details right away-- specifically if they're asking for money-- erase the message right away!! Maybe a scam artist trying to deceive you right into giving up sensitive details similar to this so they can steal your identity as well as run up costs on your credit cards or checking account later on down.
Just how to quit email spam
Email spam can be quit with an excellent filter. Your e-mail supplier must have a spam filter built-in, but if you use a third-party tool, it needs to be able to detect most harmful e-mails.
Malware or infection spam is an infection camouflaged as an innocent email. It normally arrives as an add-on or web link to a malicious internet site, which might contaminate your computer if you click on it.
Malware can be come by downloading an antivirus program as well as running normal scans on your computer system. Antivirus programs are cost-free online, although some may need settlement for more advanced functions such as real-time scanning as well as automated updates.
You can also secure your computer by installing an adblocker like uBlock Origin or AdBlock Plus (both readily available free of cost). These programs prevent malvertisement from filling on sites, stopping them from contaminating your computer system when clicked by chance.
Social media spam
Social media site spam is the name provided to a wide variety of tasks created to control social media sites systems for the benefit of the spammer.
Social network spam can be split right into two main categories known as 'material' as well as 'interaction'.
Web content spam is when a person blog posts web content on a platform (such as Twitter or Facebook) to drive website traffic in other places. This may be a link to an external internet site, a call-to-action or even just a message with no web link. Material spammers often utilize this strategy to rank very in Google's search engine result, although they can also be made use of by web designers who intend to enhance their own site's rankings in Google's index.
Engagement spam is when somebody utilizes social media platforms to increase the variety of likes, retweets or shares they get on their posts. This may entail making multiple accounts or getting followers to give the impact that there is more rate of interest in what they are posting than there is.
The most effective techniques of dealing with social networks spam are:
Record the account to Facebook: Facebook has a web page particularly for reporting spammy or fake accounts where you can select from several categories such as "fake name", "advertiser", "spam", etc. You can also report the account directly from their account web page if it's been developed recently and also hasn't had time to develop any fans or pals.
Change your settings: Social networks have different alternatives for blocking undesirable fans or communications that may assist solve several of these troubles. Facebook permits users to set up lists of buddies that just see specific points, such as private messages or images shared with them (this feature has recently been increased).
Block or unfollow them on Twitter: Twitter enables you to obstruct users and also unfollow them if they're following you (you can additionally unfollow any person who follows you if you want). This will certainly prevent them from seeing your tweets in their timeline or having the ability to talk about your own (unless they have one more account). It's simple to obstruct a person on Twitter-- simply click the "block" button when you see their tweet, as well as they will not have the ability to interact with you any longer.
Mute them: Muting someone implies that their updates will not show up in your feed (Twitter) or timeline (Facebook). You'll still have the ability to see their account information as well as blog posts when they're identified in something, yet they will not be able to interact with you. It's one way of limiting your direct exposure without blocking them entirely.
Usage third-party devices: There are additionally some useful third-party devices for handling spam on Twitter. These include Tweetdeck, Buffer as well as Hootsuite; these tools allow individuals to set up blog posts at specific times with pre-defined hashtags and manage to make sure that they don't need to maintain inspecting back frequently for brand-new content.
Comment spam
Comment spam are primarily located on web sites or blogs. It is a remark left by an automatic program or individual that leaves false info. This can either be done to advertise a product and services or merely frustrate the blog site proprietor.
Comment spamming is extremely usual and also has actually been around for several years. Many people who run their very own blogs have needed to take care of this concern eventually in their lives. While it can be very discouraging as well as bothersome, there are numerous means you can fight it and also keep it from taking place once again.
The first thing you need to do is check your blog's settings. There are choices in some blogging software that enable you to block specific IP addresses from leaving comments. Talk with someone at your hosting company so they can aid set these up for you if you're not sure just how this functions.
Another alternative is making use of an anti-spam plugin such as Akismet. These plugins will check all incoming remarks as well as immediately remove any that aren't authentic before they reach your inboxes or small amounts queues.
Trackback spam
Trackback spam is an usual type of spam found on blogs, information websites and social networks blog posts. Trackbacks are just linking back to one more blog post or webpage, so when you leave a trackback on someone's blog site, it's essentially saying: "Hey, I like this blog post a lot that I wish to inform every person about it."
The problem is that some web sites utilize trackbacks to gain useful back links from prominent websites without ever before in fact reading the web content of those websites or liking them enough to suggest them in their blog post. This is essentially what spamming is-- using any strategy to get your name or brand name out there without providing worth.
Just how Do I Stop Trackback Spam?
There are a number of methods you can quit trackback spam from occurring:
Disable Trackbacks on Your Page
If you do not desire individuals to be able to leave trackbacks on your post, you can disable this function by going into your WordPress control panel and also clicking on Settings -> Discussion. Click on the checkbox next to "Enable Trackbacks."
If you desire people to still have the ability to leave discuss your article, you can allow remarks however disable trackbacks all at once. Go into Settings -> Discussion once again, but this time uncheck both boxes under "Allow Link Notification From:" to ensure that no one can leave talk about your blog.
Utilize a plugin like ReCaptcha by Automattic.
This plugin works with Jetpack to create an extra layer of protection versus trackbacks from spammers. It will certainly ask the visitor to solve an easy mathematics issue before permitting them to leave a remark or upload a trackback on your blog. This makes it harder for spammers to abuse your site without being detected as human.
Usage Akismet by Automattic.
Both plugins use expert system (AI) to recognize spam remarks and quit them prior to they appear on your site. Nonetheless, both plugins likewise have their constraints-- Spam Karma only works with WordPress.com blog sites. In contrast, Akismet only deals with self-hosted WordPress sites with comments enabled as well as Akismet Premium enabled (costs $5 per month).
Browser spam
Web browser spam is a sort of spam located on internet browsers. Browser spam is a kind of advertisement that shows up on a person's screen without their authorization or expertise. Web browser spam can impact any internet browser, consisting of Google Chrome, Mozilla Firefox as well as Internet Explorer.
Browser spam might appear in different means relying on the web browser being utilized. For example, if you are utilizing Google Chrome as well as searching Facebook, web browser spam could be a promotion for one more social media sites site that pops up on your screen. This advertisement will typically have nothing to do with what you were formerly checking out and also will sidetrack you from what you were doing prior to it popped up.
The very same goes with various other internet browsers made use of by lots of people worldwide, such as Internet Explorer as well as Mozilla Firefox. Due to the fact that they take up area on your display as well as disrupt whatever you are doing prior to they reveal up, these advertisements are commonly aggravating.
Browser hijacking
Web browser hijacking is a kind of malware that permits cybercriminals to take over your online search engine and web page. The software application involved in this kind of attack is called an internet browser hijacker, which describes any kind of program that changes the settings in your internet browser without your permission. These programs can hijack your internet browser to show undesirable advertisements as well as produce profits for the makers.
One of the most usual types of web browser hijackers are extensions and also toolbars, yet web browser hijackers can likewise be set up as part of other types of malware, such as ransomware. When they download and install an infected documents or open e-mail attachments from unknown senders, browser hijackers are usually mounted without the customer's understanding.
Exactly How to Remove Browser Hijackers
If you've discovered odd practices from your internet browsers, such as redirections and pop-up advertisements, you may be infected with a web browser hijacker. Hijackers are programs that alter your web page and also search engine setups without your approval. They can additionally change the default internet search engine, insert unwanted toolbars as well as adware, or perhaps take your individual information.
To get rid of a browser hijacker, adhere to these actions:
Disable expansions:
Most likely to Settings on Windows or Preferences on Mac.
Try to find an icon identified Extensions or Add-ons. Click More Options at the bottom of the home window and look for a similar food selection item if you do not see this alternative right away readily available.
Once you find it, click Disable beside any kind of extensions you intend to disable.
Utilize an anti-malware program:
You may have been contaminated by malware if your internet browser is pirated and also you haven't downloaded and install anything. To get rid of malware from your computer system, make use of Malwarebytes to check for and remove malware. You can additionally use HitmanPro.com to scan for as well as eliminate active malware on your computer!
Conclusion
We hope we've given you some insights right into shielding yourself from spam. These tips aren't rocket science, yet you can reduce your opportunities of falling into these traps and also tools by using them to your everyday surfing and also online activities. If you're working in a workplace atmosphere, make sure all of your employees are aware of these tips also-- you do not wish to be the one who's liable for the following large safety breach! Now if you want to know about mobile friendly web site's in detail check out our blog site mobile-friendly web site: exactly how & why you need to make them.
Spam is made to get your attention, so check the subject line of any email you get very carefully before opening it. Browser spam is a type of spam discovered on internet browsers. Web browser spam can influence any web browser, including Google Chrome, Mozilla Firefox as well as Internet Explorer.
Web browser spam may appear in different ways depending on the internet browser being made use of. If you are using Google Chrome and surfing Facebook, web browser spam could be a promotion for another social media website that stands out up on your screen.